SecKonnect replaces outdated VPNs with a plug-and-play, credential-free hardware edge device — engineered for compliance, resilience, and zero-trust remote access from day one.
Engineered for Compliance Across
Remote work has changed — but the access stack hasn't. Unmanaged devices, VPN vulnerabilities, performance bottlenecks, and compliance pressure are converging into a serious risk for modern enterprises.
VPNs remain one of the most exploited entry points in modern enterprise breaches.
Phishable usernames, passwords, and shared secrets that travel with the user.
One successful login and an attacker has lateral movement across your entire network.
Traditional VPNs offer no defense against ransomware or zero-day exploits in the wild.
Limited session telemetry leaves IT teams blind during active incidents and audits.
Centralized concentrators degrade performance and frustrate distributed teams.
SecKonnect is a hardware-rooted Zero Trust platform that replaces outdated VPNs — simple, scalable, and resilient for today's remote enterprises.
A purpose-built Zero Trust dongle that needs no software install or agent on the endpoint.
No passwords, no shared secrets, no phishing surface. Identity is hardware-bound from the chip up.
Mutual TLS over hardware-rooted keys. End-to-end encryption that traditional VPNs simply can't match.
Instantly revoke access from a single admin panel. One click, every session terminated.
Identity, role, and time-based access — natively integrated, with no extra licensing.
Every session, every device, every action — streamed live to your admin panel for full auditability.
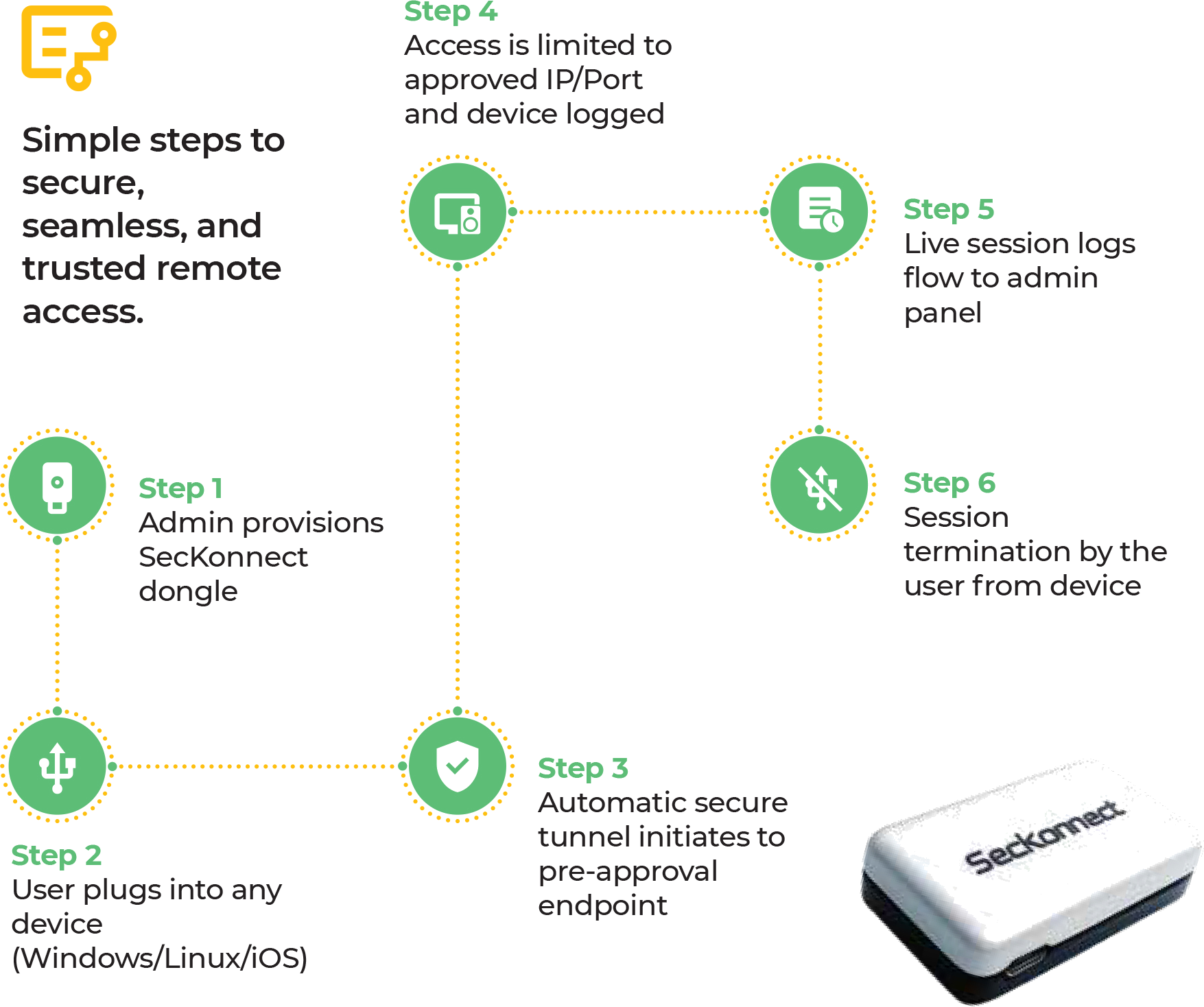
From dongle provisioning to session termination — SecKonnect's flow is designed for IT teams that need control and end-users who just want it to work.
 USB-C · 5V/2A
Passive cooling vents
Embossed brand mark
USB-C · 5V/2A
Passive cooling vents
Embossed brand mark
A premium polycarbonate housing protects a quad-core SoC, hardware secure element, and Wi-Fi 6 radio — engineered to sit quietly on a desk and disappear into your workflow.
Smaller than a deck of cards. Travels in any laptop sleeve.
Sealed enclosure with passive cooling — no fans, no moving parts.
Cryptographic keys live in tamper-resistant silicon — never extractable.
Single USB-C cable. Tunnel comes up before you finish your coffee.
Eight critical capabilities. One clear winner. See why security and IT leaders are migrating off legacy access stacks.
| Capability | Traditional VPN | SecKonnect |
|---|---|---|
| Authentication | Uses credentials | Cred-free, hardware-bound |
| Device Verification | No device validation | Device identity logged |
| Zero Trust Compatibility | Not aligned | Natively built for Zero Trust |
| Network Exposure | Entire network | Only target IP/port |
| Setup | Software agent / config | Plug-and-play, no installs |
| Access Revocation | Manual process | 1-click remote kill switch |
| Auditability | Limited session logs | Real-time session monitoring |
| Compliance Support | No native compliance | Built for ISO 27001, SOC 2, GDPR, NIST |
SecKonnect doesn't just replace your VPN — it eliminates a category of operational risk while reducing the support and infrastructure burden on your IT team.
Low support overhead
No software installs
No open ports or IP exposure
No shared VPN credentials
Continuous productivity
The SecKonnect device is a quad-core, Wi-Fi 6 capable hardware edge — passively cooled, USB-C powered, and built to disappear into the workflow.
 Request Datasheet
Request Datasheet
SecKonnect was designed alongside the controls regulators actually evaluate. Every session is logged, every device is verified, and every key lives in hardware.
A quick rundown of the questions security and IT leaders ask before piloting SecKonnect. Need more detail? See the full FAQ →
Tell us about your environment. We'll set up a personalized demo and a 30-day pilot scoped to your team.